
Telescope automatically vizualizes your company's customized security governance in real time so you can reduce your cyber risk, faster.
Demonstrably more secure, faster
An Open Source Project Supported by Red Hat
Security Operations
Security Operations is an important component of proactively preparing for and responding to cyber incidents. Some capabilities in this space include log aggregation, incident and event management, orchestration and response automation, behavioral analytics, and forensic examination and incident response.
Data Security
Organisations should provide safeguards to secure all valuable information. Data security capabilities can include the use of data classification techniques, data protection, data access controls and data availability.
Infrastructure Security
Ensuring that your platforms are up to date, patched, and suitably hardened are critical towards creating infrastructure security.
Code Security
Employing best practices around code security, (application and infrastructure-as-code), will allow teams to quickly identify and protect against malicious activity against their products.
Integration Security
There are many moving parts within modern IT platforms. The way these components interact should be secure, authenticated, documented, and protected.
Getting Involved
As an Open Source project, please feel free to jointly develop Project Telescope along with the Red Hat team.
Check out our Github Organisation
The above mentioned capabilities are the Project Telescope team's opinionated view on minimum viable security in modern ecosystems. However, any organization utilizing Project Telescope should weigh their own risk profile and technology estate when determinig MVP security requirements. Fortunately, Project Telescope is a fully-extensible project, whereby organization's can add, alter, or remove capabilities as they see fit.
Project Details
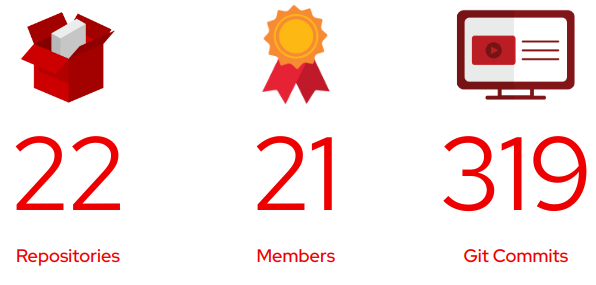
As of 6th March, 2023